-
Posted: May 11, 2026Read more »
Most security companies don’t have a CEU problem until they need to verify their records.
Technicians complete their hours, certificates are issued, and everything appears in order. The issue surfaces when those records need to be confirmed, whether for a renewal, an audit, or a client request. What seems organized at a glance often requires time to validate, and that is where gaps start to show.
For many companies, CEU management begins informally. Training is completed, certificates are saved, and someone maintains a record. That approach can work for a small team or a single state, but as the business grows, consistency becomes harder to maintain. SecurityCEU.com brings structure to that process by keeping training and records aligned in one place.
The Issue Isn’t Training. It’s Visibility
The underlying challenge is not whether training is completed, but whether it can be clearly verified at any given moment. A technician may finish the required hours, but if those records are incomplete
-
Posted: May 11, 2026Read more »
Most security companies do not notice when compliance shifts from a background task into a business constraint. The transition is gradual, and because of that, it often goes unaddressed until it starts affecting operations.
Early on, the process feels manageable. Licenses are tracked, certificates are stored, and renewals are handled as they come up. That structure can hold for a while, especially when the team is small and operating in a limited number of jurisdictions.
As the business grows, the same approach begins to create friction. More technicians, more licenses, and more regulatory requirements introduce a level of complexity that manual systems are not built to handle. What once felt organized starts to require constant attention, and compliance begins to influence how efficiently the business can operate.
At that point, it is no longer an administrative task. It is part of the operational load.
Where Compliance Starts to Impact Operations
The impact is not always obvious at
-
Posted: May 11, 2026Read more »
In the security, fire, and life safety industries, continuing education is part of the job. CEUs keep licenses active, but staying compliant is only one piece of the equation. What matters just as much is whether that training actually holds up once a technician is in the field.
Too often, it doesn’t. Courses get completed, certificates are issued, and nothing really changes in how the work gets done. When training is built around approval requirements instead of real application, it creates a gap between what is taught and what the job actually demands.
SecurityCEU.com was built to close that gap by aligning training with how technicians work, not just what regulators require.
Where Most Training Breaks Down
A lot of CEU content is designed to satisfy broad requirements, which means it rarely reflects the complexity of modern systems. Technicians are working with integrated platforms, networked devices, and evolving standards, yet the training they receive often lags behind that reality.
-
Posted: May 10, 2026Read more »
In the security industry, compliance has a reputation for being tedious. Most dealers and integrators treat it like a checklist: keep up with CEUs, renew licenses, track expiration dates, and hope nothing slips through the cracks. It is the kind of administrative burden no one wants but everyone has to deal with.
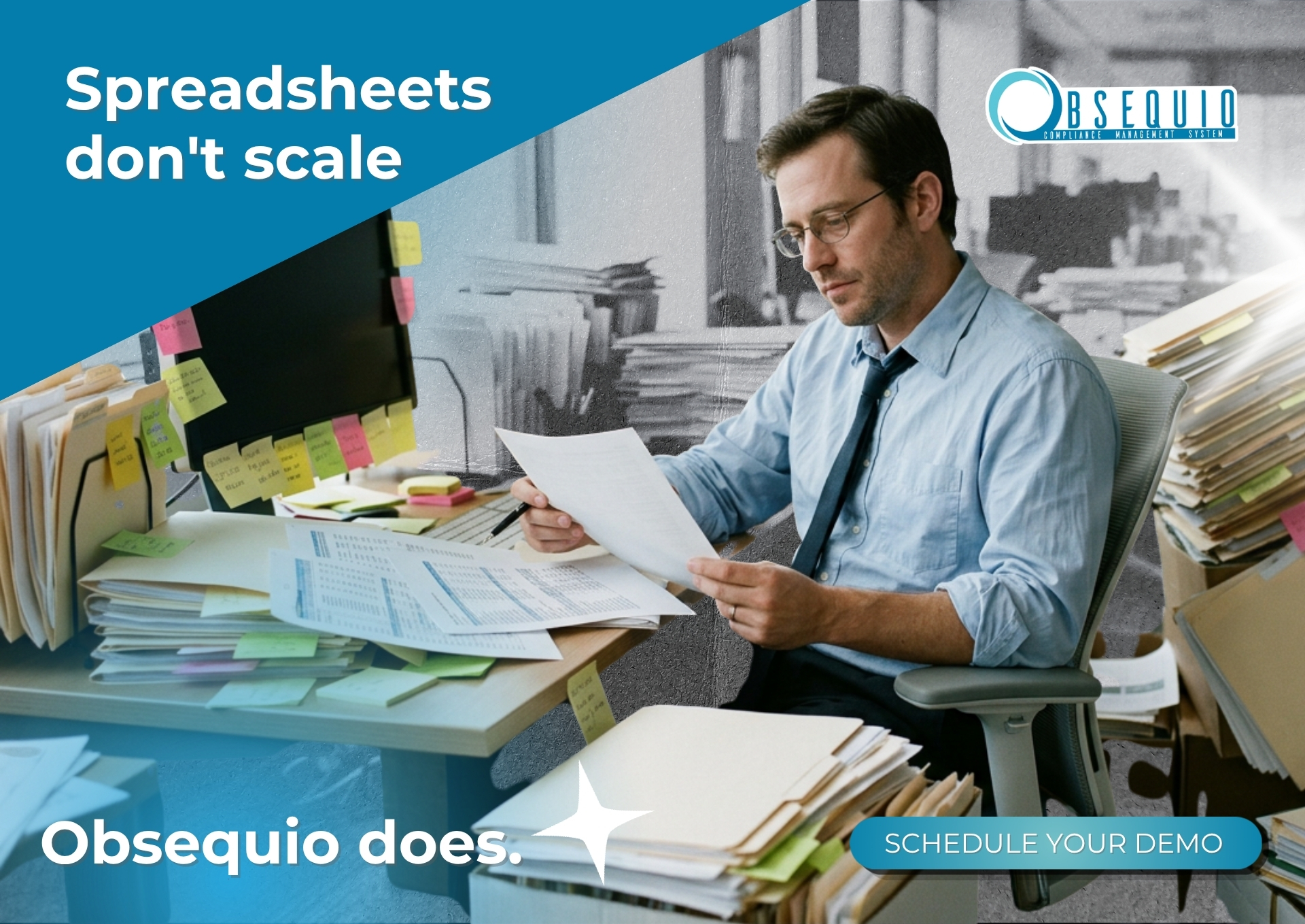
The problem is that this checklist mindset comes with a cost. When compliance is managed manually through spreadsheets, sticky notes, or disconnected files, it eats into time, accuracy, and profitability. What should be a streamlined, automated process turns into hours of tracking and guesswork that pull attention away from growth and service delivery.
That is exactly why Obsequio exists, to turn compliance management from a recurring headache into a real business advantage.
Why Spreadsheets Fail Growing Companies
When you are a small operation, spreadsheets might seem good enough. But as soon as you start scaling, adding new technicians, licenses, or states, the cracks show.
Renewal -
Posted: May 07, 2026Read more »
Compliance in the security, fire, and life safety industry is not optional. It keeps technicians licensed, businesses legal, and contracts enforceable. The problem is that most companies still manage compliance with outdated, error-prone methods that cost more than they realize.
Spreadsheets, sticky notes, inbox reminders, and filing cabinets may look cheap on paper. In reality, they drain time, money, and resources that could be used to grow the business. That is exactly why Obsequio exists.
The True Cost of Manual Compliance
Every state has its own licensing rules. CEU hours, false alarm training, background checks, and insurance renewals all stack up. Multiply that by multiple states and dozens of technicians, and the workload grows until something breaks.
Manual systems cannot keep pace. One missed deadline can trigger:
Fines and penalties that cut directly into revenue
License suspensions that sideline technicians
Lost contracts when a lapsed license removes you from consideration
-
Posted: May 07, 2026Read more »
Most security companies assume they are prepared for an audit until they are forced to prove it.
On a typical day, operations feel stable. Licenses appear current, technicians are working, and projects move forward without interruption. The difference shows up when documentation is requested and the process slows down. Records need to be located, timelines confirmed, and gaps start to surface.
Compliance may be in place, but that does not mean it is organized in a way that holds up under scrutiny. Obsequio was built to close that gap by giving security companies a structured system that keeps compliance visible, current, and ready to verify.
Compliance vs. Audit Readiness
The distinction between compliance and audit readiness is where most companies run into trouble. Meeting requirements is one thing. Demonstrating that those requirements have been met, clearly and without delay, is something else entirely.
When information is spread across different systems, even a compliant organization
-
Posted: May 06, 2026Read more »
Most security companies don’t think they have a compliance problem. They have a spreadsheet, a shared calendar, and someone who keeps an eye on renewal dates. That setup feels organized until the workload expands or the requirements shift. At that point, small gaps start to show. Obsequio was built to eliminate those gaps by replacing scattered tracking with a structured system that holds up as the business grows.
The Problem Isn’t Effort. It’s Structure
Compliance is not being ignored. It is being handled in pieces. Licenses are tracked in one place, CEUs in another, documents somewhere else, and reminders tied to individual calendars. That approach depends on consistency from multiple people and leaves room for error whenever something changes or gets missed. A single oversight can put a technician out of compliance or delay a project tied to that license.
Why Manual Compliance Fails at Scale
As companies expand across states, the complexity increases in ways that basic tools cannot
-
Posted: May 05, 2026Read more »
Every security company reaches a point where compliance is no longer theoretical. It shows up when an audit is scheduled, a contract is on the line, or leadership needs a clear answer on licensing status across the team.
That is when a simple question gets asked. Are we fully compliant right now?
For many organizations, the answer is not immediate. It has to be assembled. Teams start digging through emails, shared drives, and disconnected records to piece together a picture that should already be clear. What looked organized under normal conditions quickly turns into uncertainty. The problem is not a lack of effort. It is a system that only works when nothing is being tested.
Compliance That Breaks Under Pressure
Most companies believe they have compliance handled because the basics are covered. Renewals get submitted. CEUs are completed. Documentation exists somewhere in the business.
That sense of control holds until the moment visibility matters.
When requirements need to be verified
-
Posted: May 04, 2026Read more »
Growth in the security, fire, and life safety industry is rarely limited by demand. There are always new contracts, new territories, and new opportunities to pursue. What holds companies back is something far less visible: the ability to stay compliant while scaling.
At a certain point, adding more technicians, expanding into new states, and taking on larger projects stops being a sales challenge and becomes an operational one. Licensing requirements multiply, CEU tracking becomes harder to verify, and documentation spreads across systems that were never designed to manage it. What once felt manageable starts to slow everything down.
This is where compliance shifts from a background task into a defining factor in how far a business can go, and where platforms like Obsequio begin to separate companies that scale from those that stall.
Growth Exposes What Manual Systems Cannot Handle
Most companies do not notice the strain at first. A spreadsheet still tracks licenses, email reminders still